New Quantum Computing Advances Heighten Threat to Elliptic Curve Cryptosystems
Building a utility-scale quantum computer capable of breaking one of the most vital cryptosystems—elliptic curves—does not require the extensive resources previously anticipated, according to two independently published whitepapers. These findings signal significant progress in the race toward cryptographically relevant quantum computing (CRQC), a development that could have profound implications for digital security. The advancements are primarily driven by innovative quantum architectures and increasingly efficient algorithms designed to leverage the power of quantum mechanics for complex computations.
The urgency surrounding CRQC stems from the potential for quantum computers, armed with algorithms like Shor’s, to render current public-key cryptography obsolete. Shor’s algorithm, first theorized in 1994, demonstrates that quantum computers can factor large numbers and solve the discrete logarithm problem in polynomial time, a feat far beyond the capabilities of even the most powerful classical computers. This directly threatens cryptosystems like RSA and Elliptic Curve Cryptography (ECC), which form the backbone of secure communication and transactions across the internet, including blockchain technologies.
Neutral Atoms: A New Frontier in Quantum Computing
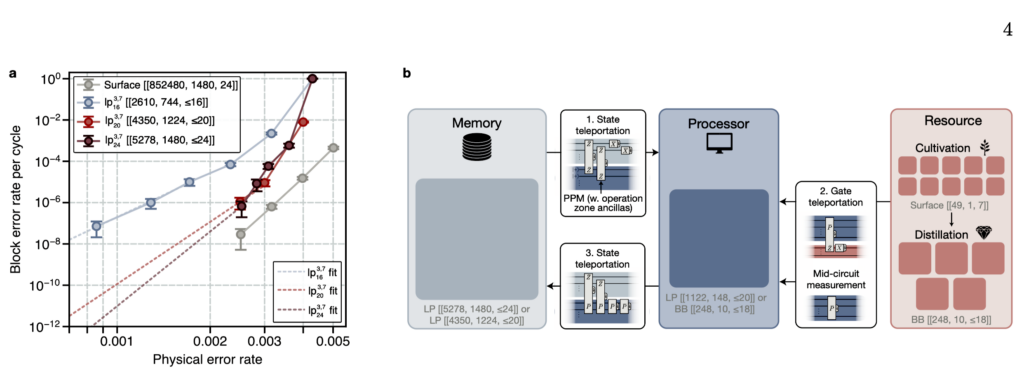
One of the groundbreaking papers details a novel approach to building fault-tolerant quantum computers using neutral atoms as qubits. This method offers a significant advantage over more traditional superconducting qubit architectures. Researchers have demonstrated that by trapping individual atoms in precisely controlled laser beams, known as "optical tweezers," they can create reconfigurable qubits that have direct access to each other. This "non-local" interaction capability is crucial for efficient error correction.
Unlike superconducting qubits, which are typically arranged in a 2D grid and can only interact with their immediate neighbors, neutral atom qubits can communicate across greater distances. This facilitates more comprehensive and efficient fault-checking mechanisms, a critical component for building reliable quantum computers. The researchers estimate that their neutral atom approach could enable a quantum computer to break 256-bit elliptic-curve cryptography (ECC) in as little as 10 days, requiring an estimated 100 times less overhead than previously thought.

The paper, titled "Shor’s algorithm is possible with as few as 10,000 reconfigurable atomic qubits," suggests that fewer than 30,000 physical qubits could be sufficient for this task. This figure represents a substantial reduction compared to earlier estimates. Complementing these theoretical advancements, a separate research team last year showcased the ability to construct neutral atom trapping arrays exceeding 6,000 qubits, indicating tangible progress in scaling these systems. The researchers involved in the neutral atom approach emphasize that while significant engineering challenges remain in integrating these components into a fully functional apparatus, their findings underscore the potential of neutral atom architectures for realizing CRQC.
Google’s Breakthrough in Blockchain Security
In a parallel development, researchers at Google have published findings detailing a method to break ECC-securing blockchains, such as those used by Bitcoin and other cryptocurrencies, in under nine minutes. This achievement also represents a substantial reduction in required resources, with the researchers reporting a 20-fold decrease compared to previous estimates.
Google’s team focused on breaking the secp256k1 elliptic curve, the cryptographic foundation for many blockchain applications. They have developed quantum circuits that can solve the elliptic-curve discrete logarithm problem with remarkable efficiency. One proposed circuit requires fewer than 1,200 logical qubits and 90 million Toffoli gates, while another needs approximately 1,450 logical qubits and 70 million Toffoli gates. A logical qubit, it is important to note, is a fault-tolerant unit encoded using hundreds or even thousands of physical qubits. The researchers estimate that their quantum machine would need around 500,000 physical qubits to achieve this, a significant reduction from previous estimates for breaking similar cryptographic standards, such as 2048-bit RSA.
A notable aspect of Google’s research is its decision to withhold the specific algorithmic improvements that enable this breakthrough. Instead, the company has released a zero-knowledge proof, a cryptographic technique that mathematically validates the existence of the enhancement without revealing its underlying mechanics. This decision, the researchers explained, is a response to the escalating risk that detailed cryptanalytic blueprints could be weaponized by malicious actors. They believe it is now a matter of public responsibility to share refined resource estimates while withholding the precise details of the attacks. This policy shift, which involved consultation with the U.S. government, marks a departure from Google’s historical stringent disclosure practices, such as those pioneered by its Project Zero initiative.
Implications and Expert Reactions
The implications of these advancements are far-reaching. The accelerated progress in quantum computing capabilities suggests that the timeline for cryptographically relevant quantum computing (CRQC) may be shorter than many had assumed. This has intensified the debate and urgency surrounding the transition to post-quantum cryptography (PQC) standards, which are designed to be resistant to attacks from both classical and quantum computers.
Brian LaMacchia, a prominent cryptography engineer and former overseer of Microsoft’s post-quantum transition, commented on the significance of these papers. He stated, "The research community continues to make steady progress on both the physical qubits and the quantum algorithms necessary to realize an efficient and practical CRQC. I don’t think either paper gives us a new, hard date for when we’re going to have a practical CRQC (which of course we’ve never had), but they both provide evidence that we are continuing to march down the road to a realizable CRQC and progress toward that goal is not slowing down."
However, not all reactions have been uniformly positive regarding Google’s disclosure strategy. Some experts, like Matt Green, a cryptography professor at Johns Hopkins University, have expressed skepticism. Green argued, "I think it’s alarmist to claim an immediate security risk from an algorithm that requires a computer that doesn’t exist. Given that the stakes here are so low (for the same reason) I’d classify it as less harmful, and more on the hype side. I think it’s more of a PR trick than a serious concern anyone has."
Concerns have also been raised about Google’s focus on the impact of CRQC on cryptocurrencies, potentially overshadowing the broader threat to other critical infrastructure. LaMacchia echoed this sentiment, stating, "While CRQCs certainly do pose a threat to blockchain-based technologies based on classical ECC algorithms, they are just one of many systems in our modern world that need to transition quickly to PQC. Especially when reading some of the policy proposals at the end of the white paper, I am just dumbfounded that Google is focused on policy frameworks for solving problems that seem unique to the cryptocurrency space (e.g., salvaged digital assets) and not the general threat that CRQC pose to all our systems that use public-key cryptography."

The Road Ahead: A Call for Proactive Transition
The convergence of these research breakthroughs highlights the critical need for organizations and governments worldwide to accelerate their transition to post-quantum cryptographic standards. While a fully realized, utility-scale quantum computer capable of widespread cryptographic breakage may still be some years away, the rapid pace of innovation suggests that preparedness is paramount. The development of robust and secure PQC algorithms, along with their widespread implementation, is essential to safeguard digital communications, financial transactions, and sensitive data against future quantum threats. The race to quantum supremacy has direct and tangible implications for global cybersecurity, and the recent advancements serve as a stark reminder that the future of secure digital infrastructure depends on proactive adaptation and rigorous research.