Russian Military’s APT28 Group Leverages Compromised Routers in Widespread Espionage Operations
The Russian military is once again engaging in extensive operations, compromising home and small office routers to redirect unsuspecting users to malicious sites designed to harvest passwords and credential tokens. These credentials are then exploited for espionage campaigns, according to a recent analysis by researchers at Lumen Technologies’ Black Lotus Labs. The sophisticated tactics employed by the group, known as APT28 and identified as a component of Russia’s military intelligence agency, the GRU, highlight a persistent and evolving threat to global cybersecurity.
Scope of the Attack and Key Findings
An estimated 18,000 to 40,000 consumer routers, predominantly from manufacturers MikroTik and TP-Link, across 120 countries have been co-opted into infrastructure controlled by APT28. This vast network of compromised devices is being used as a springboard for further malicious activities. APT28, a persistent threat actor with a documented history spanning at least two decades, is responsible for numerous high-profile cyberattacks targeting governments worldwide. The group is also recognized under a variety of aliases, including Pawn Storm, Sofacy Group, Sednit, Tsar Team, Forest Blizzard, and STRONTIUM, underscoring its multifaceted and long-standing operational presence.
The Lumen Technologies report, titled "FrostArmada – Forest Blizzard: DNS Hijacking," details how a subset of these compromised routers served as proxies. These proxies were instrumental in enabling access to a significantly larger number of routers belonging to foreign ministries, law enforcement agencies, and other government entities that APT28 sought to monitor. By controlling these routers, the group manipulated DNS (Domain Name System) lookups for specific websites. This included domains associated with Microsoft’s 365 services, a critical finding highlighted by Microsoft itself in prior advisories regarding similar SOHO (Small Office/Home Office) router compromises leading to DNS hijacking and adversary-in-the-middle attacks.
Technical Sophistication Meets Proven Techniques
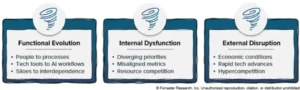
Researchers from Black Lotus Labs emphasized APT28’s adeptness at combining cutting-edge tools with established, tried-and-true attack methodologies. This dual approach allows the group to consistently refine its tactics and remain ahead of defensive measures. The report noted, "Known for blending cutting-edge tools such as the large language model (LLM) ‘LAMEHUG’ with proven, longstanding techniques, Forest Blizzard consistently evolves its tactics to stay ahead of defenders. Their previous and current campaigns highlight both their technological sophistication and their willingness to revisit classic attack methods even after public exposure, underscoring the ongoing risk posed by this actor to organizations worldwide."
The method of router hijacking primarily targets older models that have not been updated with critical security patches, leaving them vulnerable to known exploits. Once access is gained, APT28 alters the DNS settings for select domains. Subsequently, they leverage the Dynamic Host Configuration Protocol (DHCP) to propagate these malicious DNS configurations to workstations connected to the compromised routers. When users on these affected devices attempt to visit the targeted websites, their connection is surreptitiously routed through malicious servers before reaching the legitimate destination. This "man-in-the-middle" technique allows the attackers to intercept sensitive information, including login credentials and session tokens.
A Chronology of Persistent Threats
The activities attributed to APT28 and its predecessors represent a long-standing pattern of Russian state-sponsored cyber operations. While the specific campaign detailed by Lumen Technologies is recent, the underlying methodologies and the group’s operational focus are not new.
- Early 2000s onwards: The precursor activities of what would become APT28 begin to emerge, often targeting political entities and dissidents in Eastern Europe.
- 2010s: APT28 gains significant notoriety for its involvement in high-profile attacks, including the hacking of the Democratic National Committee (DNC) in 2016, which significantly impacted the US presidential election. During this period, the group demonstrated a consistent ability to infiltrate sensitive government and corporate networks.
- Mid-2010s to present: The group’s tactics evolve to include more sophisticated techniques, such as the exploitation of IoT devices and home routers. Reports from various cybersecurity firms, including Microsoft, have consistently highlighted the use of compromised routers as an entry point for espionage and disruptive cyber operations. The use of DNS hijacking becomes a recurring theme in their operations.
- 2023-2024: The current campaign, as detailed by Lumen Technologies, represents a continuation and intensification of these router-centric espionage efforts. The scale of compromised devices and the targeting of critical infrastructure entities underscore the group’s ongoing strategic objectives. The mention of LLM "LAMEHUG" suggests an integration of newer AI capabilities into their existing arsenal, indicating an ongoing effort to enhance their operational efficiency and evasion techniques.
Supporting Data and Technical Details
The scale of the current operation is significant. Lumen’s Black Lotus Labs observed the exploitation of routers in 120 countries, a broad geographical reach that suggests a global espionage objective. The prevalence of MikroTik and TP-Link routers in this campaign is notable. These manufacturers produce widely used networking equipment, particularly in home and small office environments, making them attractive targets for attackers seeking a large attack surface.
The DNS hijacking mechanism is a particularly insidious technique. By controlling the DNS resolution process, APT28 can effectively redirect users to counterfeit versions of legitimate websites. When a user types in a URL, their device queries a DNS server to translate that human-readable address into an IP address. If the DNS server has been compromised or manipulated, it can return a malicious IP address, sending the user to a phishing site or an intermediate server controlled by the attacker. This allows for the harvesting of credentials that users might enter on what they believe to be a secure, legitimate website.
The use of compromised routers as proxies adds another layer of obfuscation. Instead of directly attacking target networks from known malicious IP addresses, the attackers route their traffic through thousands of seemingly innocuous home and small office routers. This makes it significantly harder for security professionals to trace the origin of the attacks and attribute them to the responsible actors. The compromised routers become unwitting participants in the espionage chain, making attribution a complex and resource-intensive process.
Furthermore, the mention of an LLM like "LAMEHUG" suggests that APT28 may be employing artificial intelligence to automate aspects of their operations. LLMs can be used for a variety of purposes in cyber operations, including generating convincing phishing content, identifying vulnerabilities, or even crafting sophisticated code. This integration of AI could lead to more efficient and adaptable attack campaigns.
Official Responses and Industry Reactions
Cybersecurity firms and government agencies have consistently warned about the persistent threat posed by APT28. While direct, real-time official statements regarding this specific Lumen Technologies report may not yet be widespread, the findings align with previous alerts and ongoing efforts to combat Russian-backed cyber espionage.
Microsoft, as mentioned in the report, has been vocal about the risks associated with compromised SOHO routers and DNS hijacking. Their security advisories have aimed to educate users and organizations about these threats and provide guidance on mitigation strategies.
Law enforcement agencies and national cybersecurity centers, such as CISA (Cybersecurity and Infrastructure Security Agency) in the United States and its counterparts in allied nations, regularly issue threat intelligence reports and advisories about groups like APT28. These organizations work to share information with the private sector and critical infrastructure operators to bolster defenses.
The cybersecurity research community, represented by entities like Lumen’s Black Lotus Labs, plays a crucial role in uncovering and exposing these sophisticated attacks. Their detailed technical analyses provide the foundational intelligence needed for defense and attribution efforts.
Broader Impact and Implications
The implications of APT28’s continued reliance on compromised routers are far-reaching:
- Erosion of Trust: The ability of malicious actors to hijack legitimate internet traffic erodes trust in the security of online communications and services. Users may become hesitant to conduct sensitive transactions or share information online if they fear their connections are being compromised.
- Espionage and Intelligence Gathering: The primary objective of these operations appears to be intelligence gathering. By harvesting credentials and monitoring traffic, APT28 can gain insights into government operations, strategic planning, and sensitive diplomatic communications. This can provide a significant advantage to the Russian state.
- Disruption and Sabotage Potential: While the current focus seems to be espionage, the infrastructure built through compromised routers could, in theory, be repurposed for more disruptive or destructive cyberattacks. This remains a persistent concern from state-sponsored threat actors.
- Supply Chain Risk: The reliance on commonly used networking equipment highlights a significant supply chain risk. Vulnerabilities in widely deployed hardware, whether through design flaws or lack of timely patching, can be exploited to compromise a vast number of users and organizations.
- The Need for Proactive Security: This campaign underscores the critical importance of proactive cybersecurity measures for both individuals and organizations. This includes regular software updates for all network devices, strong and unique passwords, and the implementation of robust security protocols. For businesses, this also involves network segmentation and advanced threat detection systems.
The ongoing activities of APT28 serve as a stark reminder that the threat landscape is constantly evolving. The group’s willingness to adapt its tactics, from leveraging advanced AI to revisiting classic attack methods, demonstrates a persistent and determined adversary. The widespread compromise of consumer routers, often overlooked in broader cybersecurity discussions, represents a critical vulnerability that can be exploited for significant strategic advantage by nation-state actors. Continued vigilance, robust technical defenses, and international cooperation are essential to mitigate the risks posed by such sophisticated and persistent threats.