CanisterWorm Malware’s Disruption and Evolving Threat Landscape
In an email communication on Sunday night, Aikido researcher Charlie Eriksen announced the disabling of a malicious software package, dubbed CanisterWorm by Aikido. This development marks a significant, albeit temporary, setback for the threat actor known as TeamPCP. Eriksen stated, "It wasn’t as reliable/untouchable as they expected," but acknowledged that "for a while, it would have wiped systems if infected." This swift action by researchers underscores the dynamic and often fast-paced nature of cybersecurity threats.
CanisterWorm, like its predecessors within the TeamPCP arsenal, exhibits a sophisticated targeting strategy. It infiltrates Continuous Integration and Continuous Deployment (CI/CD) pipelines, critical infrastructure for modern software development. These pipelines are designed to automate the build, test, and deployment phases of software, enabling rapid iteration and delivery. By compromising these systems, TeamPCP aims to achieve widespread propagation and impact.
"Every developer or CI pipeline that installs this package and has an npm token accessible becomes an unwitting propagation vector," Eriksen explained. "Their packages get infected, their downstream users install those, and if any of them have tokens, the cycle repeats." This mechanism highlights the inherent risks within the software supply chain, where a single compromise can cascade through multiple dependent systems and organizations. The reliance on developer tools and package managers like npm, while essential for efficiency, creates potential entry points for malicious actors.
A concerning evolution of CanisterWorm emerged over the weekend with the addition of a new payload: a data-wiping component specifically targeting machines located in Iran. This updated version of the malware incorporates a geo-fencing mechanism. Upon infecting a system, CanisterWorm assesses its geographical location by checking the machine’s timezone settings or its configured regional usage. If the system is identified as being in Iran, the malware’s behavior shifts. Instead of activating its credential-stealing capabilities, it triggers a novel wiper component, which TeamPCP developers have named "Kamikaze."
Eriksen conveyed that, as of the time of his statement, there was no concrete evidence of actual damage inflicted on Iranian machines by the Kamikaze wiper. However, he cautioned about the substantial potential for widespread disruption should the malware achieve a significant level of active spread within the targeted region. "There’s no indication yet that the worm caused actual damage to Iranian machines, but that there was ‘clear potential for large-scale impact if it achieves active spread,’" he stated. Eriksen further described Kamikaze’s operational logic as having a "simple and brutal" decision tree, implying a direct and destructive function once activated.
The inclusion of a wiper targeting Iran represents a notable departure from TeamPCP’s previously observed modus operandi. Historically, the group’s primary motivation has been financial gain, with their malware campaigns often designed to exfiltrate sensitive data for ransom or to sell on the dark web. The targeting of a country with which the United States is currently engaged in complex geopolitical relations, and the deployment of a destructive wiper with no immediately apparent financial incentive, raises questions about the group’s evolving objectives.
Aikido researchers remain uncertain about the precise motive behind this strategic shift. Eriksen elaborated on this enigma: "While there may be an ideological component, it could just as easily be a deliberate attempt to draw attention to the group. Historically, TeamPCP has appeared to be financially motivated, but there are signs that visibility is becoming a goal in itself. By going after security tools and open-source projects, including Checkmarx as of today, they are sending a clear and deliberate signal." This suggests a potential evolution from purely profit-driven operations to a more complex strategy that may encompass geopolitical signaling or a desire for notoriety within the cybersecurity community.
The Interconnected Nature of Supply Chain Attacks
The incident involving CanisterWorm is part of a broader trend of increasingly sophisticated supply chain attacks, where the security of third-party software components is exploited to compromise end-users. The recent compromise of Trivy, a vulnerability scanner developed by Aqua Security, which occurred just last week, serves as a stark example of this interconnected threat landscape.
The Trivy compromise was facilitated by a preceding security incident that affected Aqua Security itself in late February. Despite Aqua Security’s incident response efforts, which included an intended replacement of all compromised credentials, a critical oversight allowed TeamPCP to regain access. This lapse in credential management enabled the threat actors to seize control of the GitHub account used for distributing the Trivy vulnerability scanner. In the aftermath, Aqua Security stated it was undertaking a more comprehensive credential purge to prevent recurrence. This incident highlights the persistent challenges organizations face in ensuring complete and secure credential rotation following a breach.
Understanding CI/CD Pipelines and Their Vulnerabilities
CI/CD pipelines are the backbone of modern software development, enabling agile methodologies and rapid deployment cycles. They automate a series of interconnected processes, including:
- Continuous Integration (CI): Developers frequently merge their code changes into a central repository. Automated builds and tests are then run to detect integration errors early.
- Continuous Delivery (CD): This phase extends CI by automatically deploying all code changes to a testing and/or production environment after the build stage.
- Continuous Deployment (CD): This is the final stage where every change that passes all stages of the pipeline is automatically released to customers.
The efficiency gains offered by CI/CD pipelines come with inherent security risks. These systems often have broad access to sensitive resources, including code repositories, cloud infrastructure, and authentication tokens. A compromise within a CI/CD pipeline can therefore grant attackers extensive privileges, allowing them to inject malicious code into legitimate software, steal credentials, or disrupt operations.
The vulnerability exploited by CanisterWorm lies in the package management ecosystem, particularly within the Node.js environment managed by npm. Developers often rely on third-party packages to accelerate development. If these packages are compromised, they can introduce malicious code into the development workflow. When a developer’s npm token, used for authentication and authorization with the npm registry, is accessible within an infected CI/CD pipeline, it creates a direct pathway for the malware to propagate.
The Evolution of TeamPCP and Shifting Motivations
TeamPCP, also known by other aliases such as Rocke, has been active in the cybersecurity threat landscape for several years. Their previous activities have predominantly focused on financial gain, often through ransomware attacks and the theft of cryptocurrency. Their malware has been observed to target vulnerabilities in various software and platforms, with a consistent emphasis on profiting from their illicit activities.
The introduction of the Kamikaze wiper, specifically targeting Iran, marks a significant deviation from this established pattern. Several hypotheses can be considered regarding this shift:
- Geopolitical Alignment: It is possible that TeamPCP has aligned itself with or been co-opted by state-sponsored actors or entities with specific geopolitical objectives related to Iran. This could involve an ideological motivation to disrupt Iranian infrastructure or to exert pressure on the country.
- Diversification of Tactics: Threat actors often diversify their tactics to evade detection and explore new avenues for impact. The wiper functionality could represent an attempt to expand their capabilities beyond financial extortion.
- Attention and Notoriety: As Eriksen suggested, the move might be a deliberate strategy to gain attention and notoriety. By engaging in a high-profile attack with geopolitical implications, TeamPCP could be seeking to elevate its profile within the cybercriminal underground or to attract new affiliates or sponsors.
- Testing and Probing: The wiper might also be a test of new capabilities or a probe to assess the resilience of Iranian critical infrastructure, even if widespread damage was not immediately achieved.
The fact that TeamPCP has also targeted security firms like Checkmarx and open-source projects further supports the notion of a deliberate signal being sent. By attacking the very tools and platforms designed to enhance security, they are demonstrating a willingness to challenge established cybersecurity norms and potentially undermine trust in the open-source ecosystem.
Broader Implications and Future Concerns
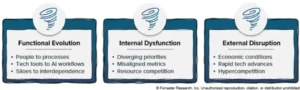
The incident involving CanisterWorm and its Kamikaze payload underscores several critical concerns for the cybersecurity community:
- The Enduring Threat of Supply Chain Attacks: The continuous targeting of CI/CD pipelines and open-source software highlights the persistent vulnerability of the software supply chain. Organizations must implement robust security measures throughout their development lifecycle, including thorough vetting of third-party dependencies, strict access controls for CI/CD systems, and continuous monitoring.
- The Blurring Lines Between Financial and Geopolitical Motivations: The evolution of groups like TeamPCP, which may be shifting from purely financial motives to incorporating geopolitical elements, complicates threat analysis and response. This necessitates a more nuanced understanding of threat actor motivations and a broader approach to cybersecurity strategy.
- The Destructive Potential of Wiper Malware: The development and deployment of wiper malware, especially with targeted capabilities, pose a significant threat to critical infrastructure and data integrity. The ease with which such malware can be developed and deployed, even by financially motivated groups, is a cause for concern.
- The Importance of Rapid Incident Response and Collaboration: The swift action by Aikido in identifying and disabling the CanisterWorm canister demonstrates the critical role of independent security research and collaboration in mitigating emerging threats. Sharing intelligence and coordinating responses are vital in staying ahead of agile adversaries.
The incident also serves as a potent reminder of the need for continuous vigilance and adaptation in the cybersecurity domain. As threat actors evolve their tactics, techniques, and procedures, so too must the defenders. The ongoing battle to secure digital infrastructure requires constant innovation, robust security practices, and a deep understanding of the ever-changing threat landscape. The ability of researchers to quickly identify, analyze, and neutralize threats like CanisterWorm is crucial, but the underlying vulnerabilities in the interconnected digital ecosystem remain a significant challenge.